Configuring server logins using SSH certificates is a great way to increase server security (brute force SSH passwords will become useless). And using a password for the private certificate will reduce the risk of key cracking (when copying the login certificate).
The instructions cover the issues of creating and configuring SSH certificates on the Ubuntu 18 and the PuTTY client application.
Contents
- Preparing folders
- Server preconfiguration
- Configuring SSH certificates on the server
- Configuring PuTTY Connection
- Final server setup
Article in other languages:
?? – Cómo configurar certificados SSH para iniciar sesión en Ubuntu
?? – Как настроить SSH сертификаты для входа на Ubuntu сервер
Preparing folders
We prepare the folder and key file on the server.
An important point when configuring SSH authorization by keys is to specify the correct Permissions for the folder and key file.
Run:
mkdir ~/.ssh
chmod 0700 ~/.ssh
touch ~/.ssh/authorized_keys
chmod 0644 ~/.ssh/authorized_keys
Server preconfiguration
Allow login using the public SSH certificate to the server and specify the path to the certificate in the SSH settings, the sshd_config.
nano /etc/ssh/sshd_config
Uncomment or add values:
PubkeyAuthentication yes AuthorizedKeysFile .ssh/authorized_keys
Configure SSH certificates on the server
Generating SSH keys.
ssh-keygen -a 1000 -b 4096 -o -t rsa
Specify the key storage path and its name.
/root/.ssh/id_rsa
? In my case, when creating a certificate for root, it turned out to be important to specify the hard path /root/.ssh/, instead of the relative ~/.ssh/, to avoid the SSH Server refused our key error.
The system will also create a public key along this path.
We set a passphrase to access the private key.
Add the contents of the public key file to the SSH authorization certificate file.
cat ~/.ssh/id_rsa.pub >> ~/.ssh/authorized_keys
Restart the SSH service.
sudo service ssh restart
Configuring PuTTY Connection
Let’s convert the private key to PuTTY key format
? When trying to use the copied key, PuTTY will show an error: Unable to use key file (OpenSSH SSH-2 private key (new format)).
- Copy the private key id_rsa (or the contents of the key to a file) to the local computer;
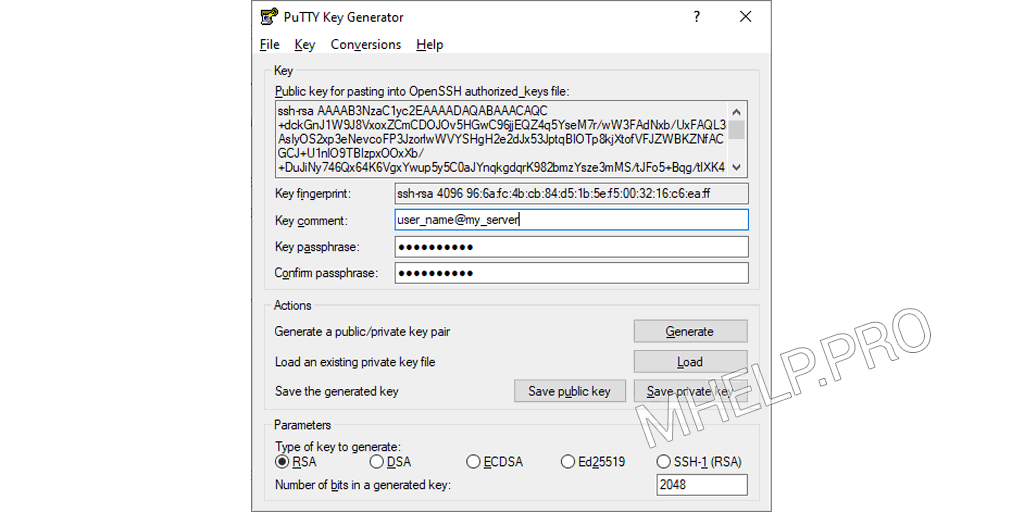
- Run the puttygen program (from the PuTTY folder);
- Click the Load button and select the private key file;
- Enter the password for the private certificate;
- Click Save private key to save the private key in the desired format (you can change the Key comment, this will not affect the operation of the key).
Configuring PuTTY connection using SSH certificate
Add the private certificate to the connection:
Connection > SSH > Auth > Private key file for authentication
If the connection is successful, after entering the username, you will be prompted for the certificate passphrase, after which the login to the server should be successful.
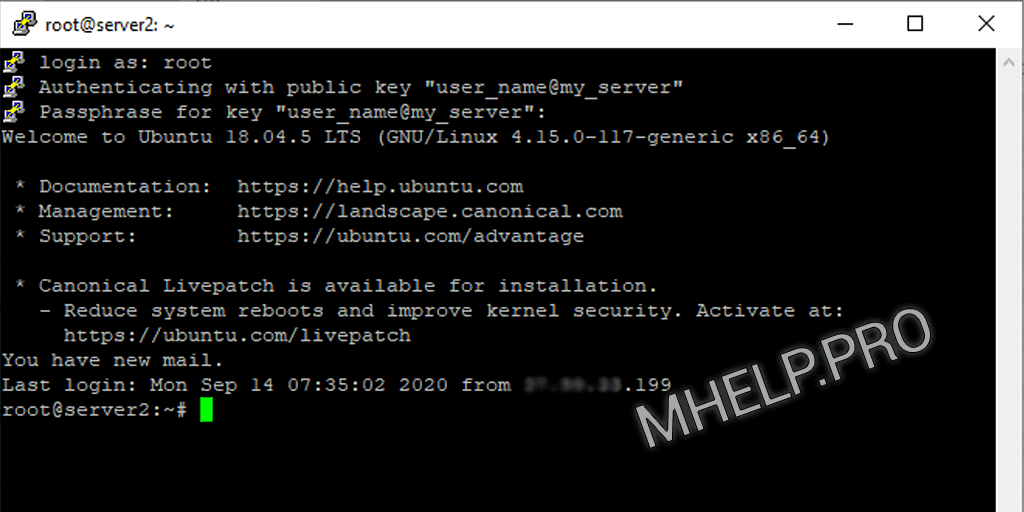
? If you get the message SSH Server refused our key when logging into the server, check that the rights to the .ssh folder and authorized_keys file are correct, and also specify the direct path to the folder with the keys at.
Final server setup
The last step in configuring SSH is to disable the ability to log into the server using a password in the configuration file.
nano /etc/ssh/sshd_config
Uncomment or add value:
PasswordAuthentication no
Then restart the SSH service.
sudo service ssh restart
Configuring authorization by SSH certificate – completed!
How to configure SSH certificates for logging into an Ubuntu server and the option to fix the SSH Server refused our key error was discussed in this article. I hope you can now set up SSH server and client logins using certificates. However, if you run into any issues while configuring SSH server and client, feel free to write in the comments. I will try to help.


How do you generate SSH keys using the “ssh-keygen” command, and what are the key options and parameters used in this process?
Your article is about setting up SSH RSA Keys and not about setting up SSH certificates. You are using the wrong terminology.
Yes, I know. It’s made specifically for search engine optimization.