Starting with RouterOS version 6.42, it became possible to block sites using TLS-Host (TLS Traffic) – this allows you to block https sites.
Article in other languages:
?? – MikroTik: Cómo bloquear un sitio (host TLS)
?? – MikroTik: Как заблокировать сайт (TLS host)
?? – MikroTik: Comment bloquer le site (TLS host)
?? – MikroTik: So blockieren Sie eine Site (TLS host)
?? – MikroTik: Hoe een site te blokkeren (TLS-host)
For example, let’s write a Facebook blocking rule.
To do this, create a rule in the firewall:
[IP] -> [Firewall] -> [+] -> [General: Chain=forward, Protocol=6 (tcp), Dst. Port=443, In. Interface=bridge1-lan)] -> [Advanced: TLS Host=*facebook.com*] -> [Action: Action=drop]
Or run in terminal:
/ip firewall filter add action=drop chain=forward dst-port=443 in-interface=bridge1-lan protocol=tcp tls-host=*facebook.com* comment="Block: Facebook.com"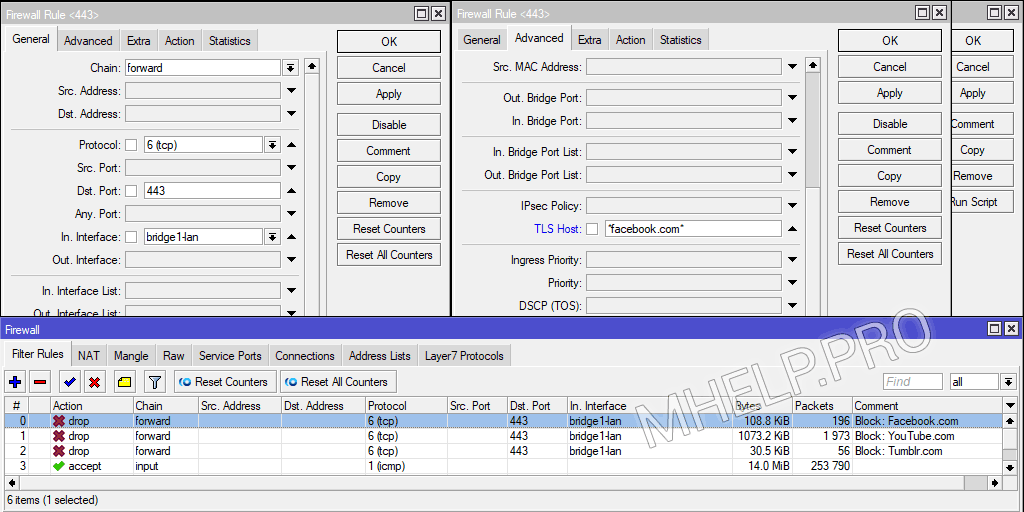
Place the rule above the permissive ones.
The rule uses the Glob syntax to describe site addresses.
This blocking method will not work if the connection to the site has already been established. Or it may not work when using FastTrack.
The TLS host blocking method is not very convenient for blocking many sites, but it can be useful in some cases.
? How to block a site using MikroTik and TLS host was discussed in this article. I hope you can now use this site blocking tool in your work. However, if you run into any problems while setting up, feel free to write in the comments. I will try to help.
The script is checked: hAP ac lite [RouterBOARD 952Ui-5ac2nD], RouterOS 6.47.8 (stable).


It seems to me that Mikrotik uses the SNI filter in TLS and most likely this method will not work with. TLS1.3.
Hello this method no longer work if using Firefox version 86 or later (DNS over HTTP is disabled), somehow Firefox privacy protection features (tracker, supercookies) make the TLS traffic can not be recognized by mikrotik. Previously we use Firefox version 84, and this tls filter work flawlessly. Thanks
Thank you very much for the information!